Certificate Fraud Is More Common Than You Think — Here's How Training Providers Can Fight Back
The Hire That Came Back to Haunt Everyone
A construction company brings on a new site supervisor. His resume lists a valid OSHA 30-hour certification, and there's a professional-looking PDF attached to back it up. Nobody calls the issuing training center to verify — why would they? The certificate has a logo, a signature, a date. It looks right.
Six months later, an incident on the job site. During the investigation, someone finally checks with the training center. The certificate is fake. There is no record of this employee ever completing the course. Now the employer faces regulatory exposure, potential liability in any legal proceedings, and the awkward task of explaining to their insurer why a supervisor with fabricated credentials was running a crew.
This is not a rare edge case. It's a pattern that plays out across regulated industries every year — quietly, because neither the employer nor the training center has any particular incentive to publicize it.
How Common Is Credential Fraud, Really?
Documented patterns of resume fraud are consistent across industries. Background verification firms that screen applicants at scale report that a meaningful fraction of credential claims — certifications, licenses, completed training programs — either cannot be verified or turn out to be misrepresented. The numbers are uncomfortable for anyone who assumes a certificate PDF is trustworthy.
The problem is especially acute in industries where certification is a regulatory requirement rather than a differentiator. Healthcare credentialing, food safety handler programs, forklift operator certification, asbestos abatement training — these are fields where a certificate isn't just a credential, it's a legal precondition for doing the job. The regulatory weight attached to them creates demand, and where there's demand, there are people willing to supply a convincing fake.
The operational mechanics of fraud here are straightforward: most certificates are issued as PDF files with a logo, a border, a signature, and a name. That's all. Replicating that document takes less than an hour with basic design software. There's no central registry. There's no verification system that actually answers. There's no QR code linking to a live database. The training center issued the original, but after that, the document is entirely on its own.
Three Parties Get Hurt — and Only One of Them Caused the Problem
The employer carries the most obvious risk. Regulatory compliance violations, legal liability if something goes wrong, and the operational cost of discovering mid-employment that someone isn't qualified to do what they claimed. In industries with strict oversight — healthcare, food service, heavy equipment operation — the consequences can extend to license suspension, regulatory fines, and civil exposure.
The legitimate graduate takes a hit that rarely gets acknowledged. When credential fraud is easy, genuine certificates lose value. An HR manager who has been burned by a fake is now suspicious of all certificates from that program. The honest person who completed the course, paid for it, put in the hours — they're now competing not just against other job candidates, but against anyone willing to spend twenty minutes with a PDF editor. Their real credential has been devalued by infrastructure that couldn't distinguish it from a forgery.
The training center often bears the strangest form of harm: brand damage for a crime they didn't commit. When fake certificates circulate bearing an institution's name and logo, every bad actor strengthens the association between that institution and fraud — even when the institution itself is entirely a victim. If they can't respond promptly to verification requests, they start to seem complicit in the ambiguity. That reputation damage compounds over time.
Why the Current System Is Built for Fraud
PDF certificates have no chain of custody. Once a document leaves a training center's email server, there is no mechanism by which anyone can tell whether what they're looking at is the original or a fabricated version.
Compare this to how financial systems handle verification. A bank card has a number, an expiry date, a security code, and — behind all of that — a live system that a merchant can query in real time to confirm the card is valid, active, and not reported stolen. The answer comes back in seconds. Nobody expects a merchant to call the bank and ask a human whether the card is real.
Certificate verification has no equivalent in most training programs. The training center is the only authoritative source of truth, but in most cases, they're functionally unreachable for routine verification — no public-facing tool, no verification URL on the certificate, no structured ID system that allows even a basic lookup. An employer who wants to verify has to find a phone number, call during business hours, explain what they're looking for, and wait. Many don't bother. That gap is where fraud lives.
Sequential certificate numbering makes the problem worse. When IDs follow an obvious pattern — cert-001, cert-002, cert-003 — a fraudster can construct plausible-looking numbers for certificates that were never issued. Non-guessable identifiers, like UUIDs or structured IDs with check digits, close that particular avenue.
What Fraud-Resistant Credentials Actually Look Like
A credential that resists fraud has four properties, all of which point to the same underlying requirement: a live connection back to the source.
Live database lookup. The certificate number points to a real record that can be queried. Not a static image, not a PDF — a database entry that either exists or doesn't. A number that returns no result is its own answer.
Real-time expiry. If a certification lapses, that fact is immediately visible to anyone checking. The certificate can't be reused six months after renewal was required.
Immediate revocation. If a certificate needs to be invalidated — because someone cheated, or the credential was issued in error — that change propagates immediately. There's no paper copy floating around that still looks valid.
A permanent, public verification URL. Every certificate should have a link that anyone can visit to confirm its authenticity. Put it on the printed copy, encode it in a QR code, include it in the email. Make verification a zero-friction act rather than an investigation.
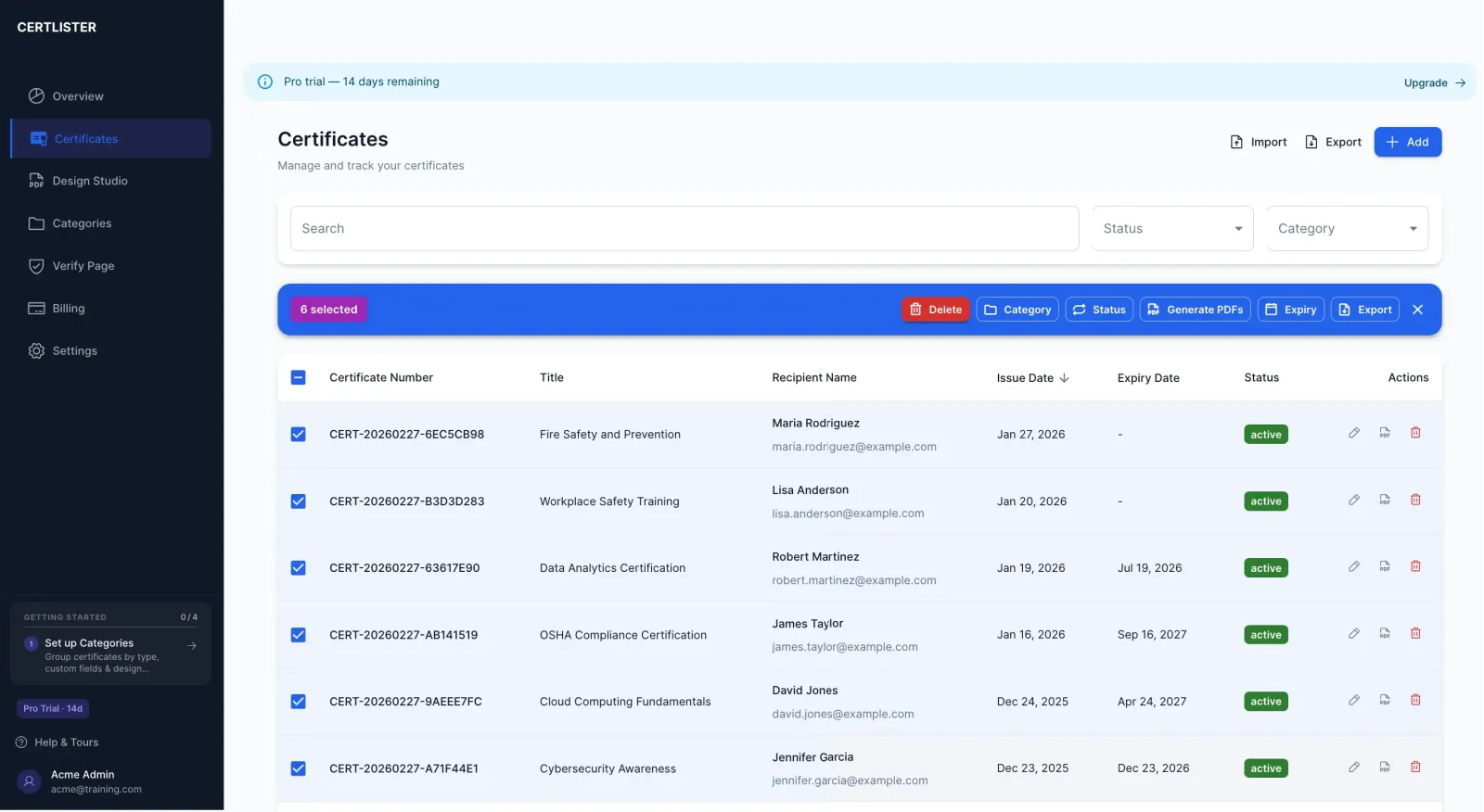
Platforms like CertLister are built specifically to provide this infrastructure — every certificate issued gets a unique number and a public verification URL, expiry dates are tracked automatically, and revocation takes effect immediately.
What Training Centers Can Do Right Now
The migration doesn't have to be complete before it starts being useful. A few concrete actions make an immediate difference:
- Switch to non-sequential certificate IDs. If you're currently issuing cert-001 through cert-whatever, move to a format that can't be guessed. This alone closes a significant fraud vector.
- Add a verification QR code to every printed or emailed certificate. Even a URL that links to a lookup page raises the barrier meaningfully. Fraudsters want easy targets.
- Implement a verification system — even a basic one. A page where someone can enter a certificate number and get a confirmed result is meaningfully better than nothing. It doesn't need to be elaborate to be effective.
- Commit to responding to verification requests promptly. If employers learn that reaching your training center gets a fast, clear answer, they'll reach out. If it doesn't, they won't — and the ambiguity serves fraud.
The Reputation Angle Is Underestimated
There's an asymmetry here worth naming directly. Training centers that make verification easy build a reputation for trustworthiness. Employers start to prefer their graduates because the credentials can be confirmed without effort. That preference compounds — it becomes a genuine competitive advantage.
Training centers that don't make verification easy get associated with fraud even when they're the victims. The inability to quickly answer "is this certificate real?" becomes, in the minds of employers, an implicit endorsement of the ambiguity. It isn't fair, but it's how reputation works.
The institutions that will thrive in industries where credential integrity matters are the ones that treat verification as a core part of what they offer — not an afterthought to paper certificates.
The infrastructure to fight certificate fraud already exists. The question is whether training centers choose to use it. Every certificate issued without a verification mechanism is a certificate that can be copied, modified, and passed off as real. Every certificate with a live verification URL is significantly harder to fake.
Fraud is opportunistic. Remove the opportunity.
CertLister is a certificate management platform built for schools and training centers. Issue professional certificates, track expiry dates, and give every graduate a permanent verification URL — no developer required. Start free →
Ready to simplify certificate management?
Join schools, companies, and training centers using CertLister. Free plan available, no credit card required.
Get Started Free